cookie
This article is a stub. You can help the IndieWeb wiki by expanding it.
cookie is a bit of data stored by the browser that gets sent with every request to a website.
Security
Cookies can have multiple optional flags set to instruct a browser what it should and should not allow to happen.
Secure: when this flag is set, the browser is told to not send this cookie unless the connection between it and the web server is secure. If your site is available on both HTTPS (secure) and HTTP (not secure) you can use this to make sure cookies containing user data are only sent to the HTTPS version, making it a lot harder for external parties to hijack e.g. login states.
HttpOnly: when this flag is set, the browser is told not to allow scripts (e.g. JavaScript) to access this cookie. This is great for things like session cookies as a browser still identifies itself with it every time it makes a request to your web server, but scripts loaded on the page cannot access or change it.
Cookie Theft/Session Hijacking is such a prevalent problem it has made it to the OWASP Periodic Table of Vulnerabilities. A lot of this can be fixed by proper use of the above optional cookie flags. “Apply Secure and HttpOnly flags” is the first rule they define for any generic cookie framework, letting the developer explicitly overwrite it if they need less security.
Note that **many frameworks default to less secure**. Example: PHP’s session cookies default to both flags turned off [1] and need a developer to turn them on, counter to OWASP’s advice.
Discussion
- Using the
Secureflag is a great way of offering a read-only version of your site without HTTPS. It will make sure no cookies are accidentally send without protection when people view the read-only version. This came up on IRC.
How to
PHP
There are two main ways cookies get used in PHP. Possibly the most important to get security right on is the session cookie.
If you have access to the server’s php.ini, you can set session.cookie-secure and session.cookie-httponly and be done. Otherwise you will need to configure your session cookies using the session_set_cookie_params-function. The function requires you to also set all the other configuration options. We can set only the Secure and HttpOnly flags with the following:
$currentSettings = session_get_cookie_params();
session_set_cookie_params(
$currentSettings['lifetime'],
$currentSettings['path'],
$currentSettings['domain'],
true,
true
);
The second method by which you are likely to use cookies is when you set them yourself using setcookie-function. The function accepts 7 arguments, and the last two are for enabling Secure and HttpOnly respectively. As an example, the following sets a cookie with the name name and the value data (arguments 3, 4, and 5 are kept as their defaults):
setcookie('name', 'data', 0, '', '', true, true);
In all cases, make sure you read the PHP manual carefully. Or depend on a framework that handles security for you.
Limiting cookies
Limiting the amount of cookies a website sets in the user's browser is one of many strategies to lower the implications of existing an upcoming regulatory privacy legislation; ideally even allowing to eliminate the need for a "cookie consent" pop-up as often required in the EU.
How to disable cookies in various applications: Matomo (formerly Piwik) in the JS code:
_paq.push(['disableCookies']);
Wordpress in functions.php
remove_action( 'set_comment_cookies', 'wp_set_comment_cookies' );
See Also
- https://www.troyhunt.com/c-is-for-cookie-h-is-for-hacker/
- For security there is also the proposed SameSite, see HTTP WG draft (and tests).
- For session cookies: The Fast Track to Safe and Secure PHP Sessions
- Directive 2009/136/EC, a.k.a. recent clarifications around the EU “cookie” law
- EU Opinion on exemptions to required consent for cookies
- Criticism: cookie consent banner blocks pages: https://twitter.com/fredbenenson/status/1127020290947436545
- "Congratulations to @FastCoDesign for one of the most egregious examples of mobile cruft I’ve ever seen. It’s actually impressive how bad this is: the initial page load manages to display zero actual content" @fredbenenson May 11, 2019
- ^^^
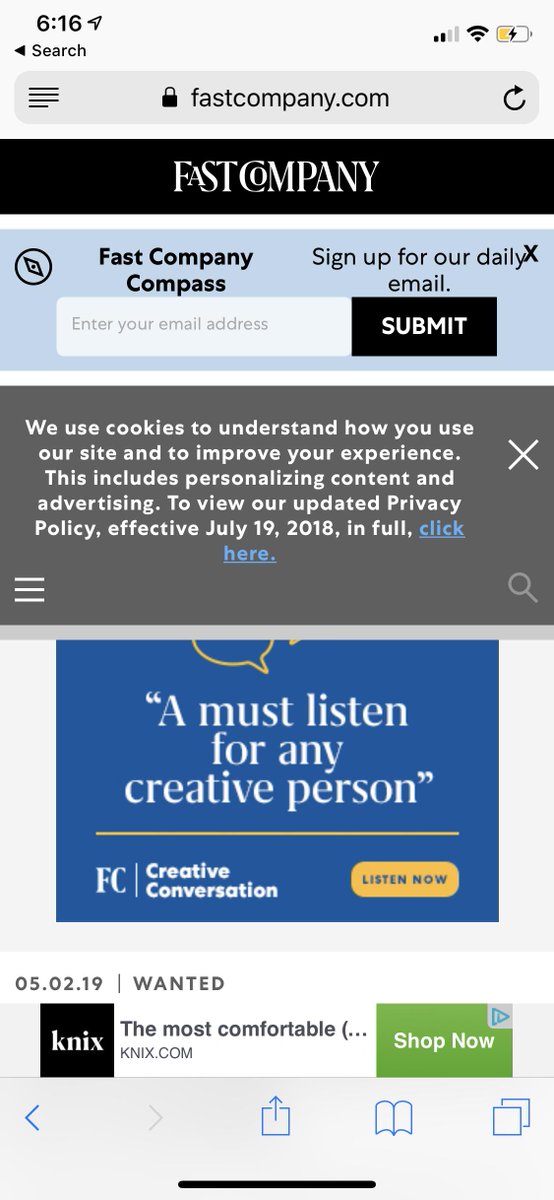
- cookie banner
