GitHub

This article is a stub. You can help the IndieWeb wiki by expanding it.
GitHub is a specialized content hosting silo for code, issues, comments, and static content that has some aspects of a commons, and through free domain mapping, a content hosting service as well.
See:
- GitHub Pages to setup a static Github pages site!
Features
- account
- organization account with membership, add/remove, roles (admin etc.)
- invitation to someone to join an organization, accepting such invitations
- profile
- elsewhere links with rel-me support
- calendar heatmap of commit history
- repository collection
- gist collection
- follow/unfollow an account
- account recovery
- organization account with membership, add/remove, roles (admin etc.)
- repository
- create new, create from existing (AKA fork) repo, delete
- unlimited public and private repositories
- has collection of code and related files with versioning
- can create pull requests in response to a repo:
- collection of edits of files submitted (like a reply) to a particular project repo
- edit a single file via the web UI and submit it as a pull request
- reply to (comment on) a pull request
- review a pull request (approve / reject, optional comment)
- stars and the ability to star/unstar a repo: serves as a personal bookmark and ranking the popularity of the repo
- follow(called "watch" in GH)/unfollow a repo: receive notifications of updates to the repo
- issues collection of issue posts
- create / edit / delete issues on (reply-to) a particular repo
- reply to (comment on) an issue
- and optionally at the same time ( Close issue ) for open issues, or ( Re-open issue ) for closed issues, if you have appropriate permissions to do so
- reacji/reaction to an issue or reply, limited to a curated set of 6, with hover text equivalents in parens:
- 👍(+1), 👎(-1), 😆(Laugh), 🎉(Hooray), 😕(Confused), ❤️(Heart), 🚀(Rocket), 👀(Eyes)
- tag-of (add a label to) an issue
- untag-of (remove a label from ) an issue
- follow/unfollow an issue
- lock/unlock an issue if you have appropriate permissions to do so
- gist
- create, edit, delete
- Atom feeds
- https://github.com/{{username}}.atom
- https://github.com/{{username}}/{{repository}}/releases.atom
- https://github.com/{{username}}/{{repository}}/tags.atom
- . . .
POSSE to GitHub
For POSSEing source code to github, see git.
While git is inherently distributed, all the extra functionality (issues, pull requests, etc.) that GitHub adds on top is not. GitHub has a nice API for interacting with repositories, which makes it pretty easy to POSSE issues, comments on issues, stars, and maybe more.
POSSE an issue
An issue post that is in reply to a particular GitHub repo can (and should) be POSSEd to GitHub as a new issue on that GitHub repo.
See examples of POSSEing issues to GitHub:
POSSE reply to repo
A reply to a GitHub repo path, may make sense to be POSSEd as a comment on that path, e.g. if it is a gist. If the reply is an issue, see above POSSE an issue.
POSSE reply to issue
A reply to a specific GitHub issue can (and should) be POSSEd as a new comment on that issue.
If the GitHub issue was itself originally posted as an indie issue, then be sure to post your reply as a multi-reply in-reply-to both that the indie issue permalink, and its GitHub copy.
POSSE reply to comment
A reply to a comment on a specific GitHub issue can (and should) be POSSEd as a comment in reply to that previous comment.
If that previous comment was itself originally posted as an indie reply, then be sure to post your reply as a multi-reply in-reply-to both that previous indie reply permalink, and its GitHub copy. E.g.:
- indie multi-reply to a comment: http://tantek.com/2018/155/t1/
POSSE star of repo
A star on a GitHub repo can (and should) be POSSEd as a like of the repo.
POSSE reacji to issue or comment
A reacji to a GitHub issue or comment can (and should) be POSSEd as a reaction to that issue/comment on GitHub respectively.
If that GitHub issue or comment was itself originally posted on the indieweb, the be sure to post your reacji as a multi-reply in-reply-to both to the indie issue/reply post permalink and their GitHub copy.
Backfeed
If you POSSE to GitHub in any of the above ways, you should backfeed any replies on your post's GitHub POSSE copy back to your own post so that you can:
- keep a copy of people's comments on your post
- view follow-ups to your post on your post, instead of having to visit GitHub's site
- reply to follow-ups to your post, from your site, instead of using GitHub's UI
- comments on issues and PRs
- emoji reactions to issues and PRs
Additional backfeed to consider implementing
- tag-of: username1 added the abc label n hours[or days] ago
- untag-of: username1 removed the abc label n hours[or days] ago
- ????: closed this in linkedPullRequest n hours[or days] ago
IndieWeb Examples
Aaron Parecki
 Aaron Parecki is automatically POSSEing comments on GitHub issues from his own site to GitHub using silo.pub (as of YYYY-MM-DD), and before that was manually POSSEing. E.g.:
Aaron Parecki is automatically POSSEing comments on GitHub issues from his own site to GitHub using silo.pub (as of YYYY-MM-DD), and before that was manually POSSEing. E.g.:
- http://aaronparecki.com/replies/2013/08/14/6/mailpile (original)
- https://github.com/pagekite/Mailpile/issues/48#issuecomment-22682787 (manual POSSE copy on GitHub)
At some point Aaron switched to using silo.pub to POSSE to GitHub
- ... need aaronparecki.com permalink of an issue/comment post in reply to github (preferably first such link after implementing silo.pub auto-POSSE to GitHub)
- ... need POSSE copy github.com permalink (that was published with silo.pub)
Colin Tedford
Colin Tedford manually POSSEs Github issues, and manually POSSEs and backfeeds comments on GitHub issues (it's just occasional bug reports, so not as onerous as it might be if he were a developer).
- http://colintedford.com/2015/02/02.0338-easy-syntax-not-working/ (original, w/ comments)
- https://github.com/glensc/dokuwiki-plugin-pageredirect/issues/18 (POSSE copy on Github)
Chris Aldrich
 Chris Aldrich is occasionally automatically POSSEing comments on GitHub issues from his Known site to GitHub. E.g.:
Chris Aldrich is occasionally automatically POSSEing comments on GitHub issues from his Known site to GitHub. E.g.:
He does this with the Known plugin to POSSE to GitHub.
Tantek
 Tantek Çelik is POSSEing to GitHub using Bridgy Publish since 2018-02-19:
Tantek Çelik is POSSEing to GitHub using Bridgy Publish since 2018-02-19:
- comments on GitHub issues (since 2018-02-19, post about)
- new GitHub issues (since 2018-02-21, post about) Main article: issue#Tantek
- replies to comments on GitHub issues (since 2018-02-21)
- multi-reply to an indie reply to a GitHub issue and its POSSE copy:
- reactions to GitHub comments (since 2018-02-24)
- reactions to GitHub issues (since 2018-02-26)
- reactions to GitHub pull requests (since 2018-07-09, same code as reactions to comments & issues)
Bridgy
Bridgy can POSSE issues, comments, stars, and emoji reactions to GitHub, as well as backfeed comments and reactions.
If you get an error POSSEing to a particular GitHub repo using Bridgy, you may need to ask the repo's organization's owner(s) to approve Bridgy as an OAuth app for that repo.
See and refer them to: https://help.github.com/articles/approving-oauth-apps-for-your-organization/
Known
Known has a plugin for automatic POSSEing to GitHub:
Silopub
- silo.pub supports creating issues, commenting on issues and pull requests, and starring repositories since 2016-04-22
PESOS from GitHub
GitHub provides atom feeds of activity on public content the following urls:
https://github.com/{{username}}.atomhttps://github.com/{{username}}/{{repository}}/releases.atomhttps://github.com/{{username}}/{{repository}}/tags.atom
Example github activity Atom feed from which you can export, PESOS or subscribe to using a feed reader:
- https://github.com/tantek.atom (for account name "tantek")
For private content, GitHub provides Atom feeds protected by a token. A users' account private feed is autodiscoverable at /dashboard: <link rel="alternate" type="application/atom+xml" title="ATOM" href="/username.private.atom?token=A54RF3F4XPIJ4TGDV2346FQWERLNUYA"/>
If you want a feed of activity by others on your repositories, it looks like you can get it through your "Personal News Feed". "Your personal News Feed shows activity—other than your own!—on repositories you watch. […] To subscribe to your personal News Feed in your favorite RSS reader, click Subscribe to News Feed under your list of repositories." https://help.github.com/articles/news-feed/
Using Github for comments
Some people use Github to gather comments for their blog posts. For each post, an issue is opened. Comments are fetched via the Github API and displayed below the blog post
Examples:
- gitment
- gitalk
- utteranc.es
- giscus - based on github discussions
- 2017-04-21 : "Replacing Disqus with Github Comments"
- jordaneldredge.com blog post and comment-tracking issue jordaneldredge.com#9
OAuth UI
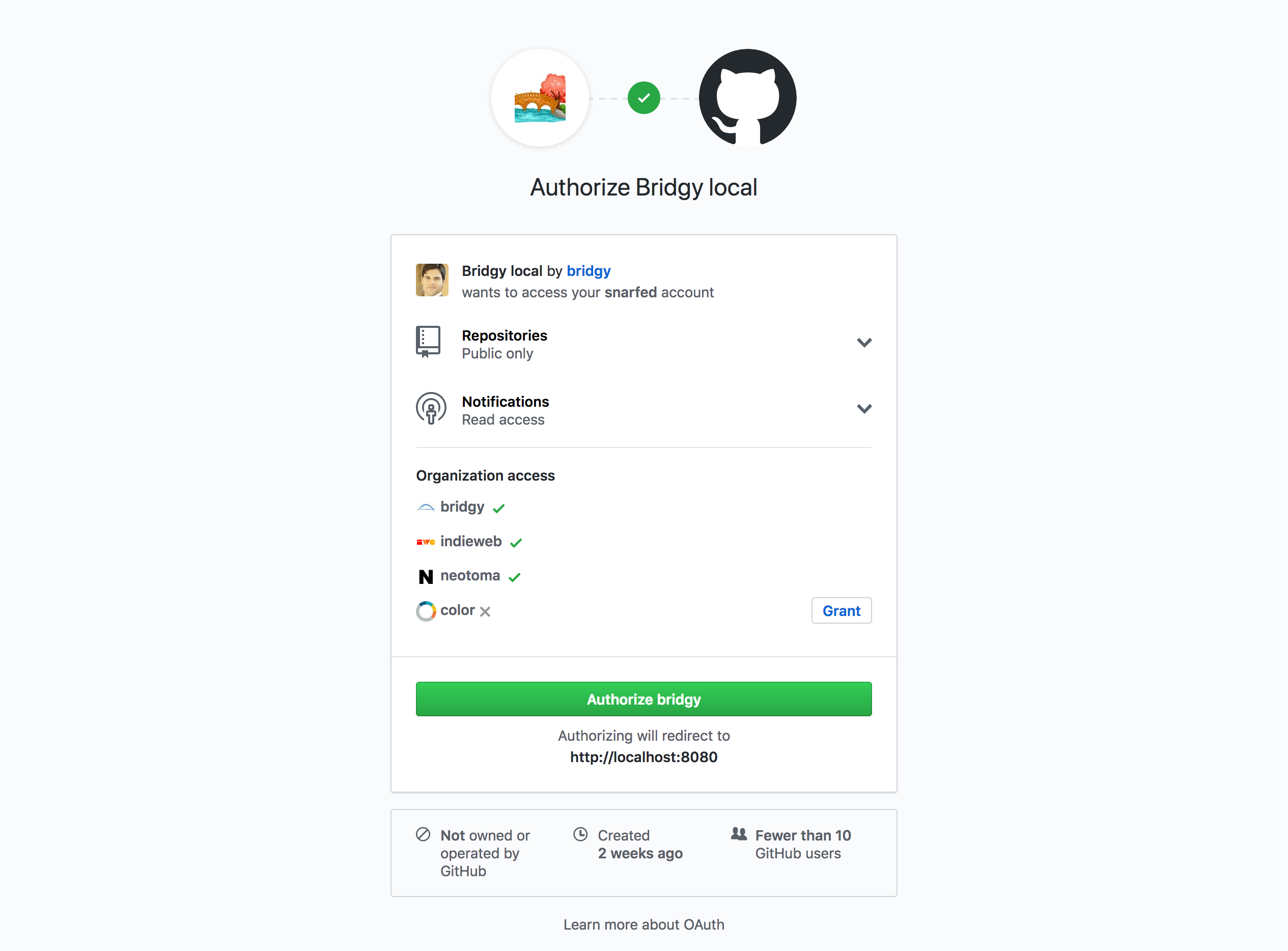
If you deploy an application that uses GitHub's API and needs to request the user's permission, it will display an OAuth permissions page that looks like *you* (the author of the application) are asking permission.
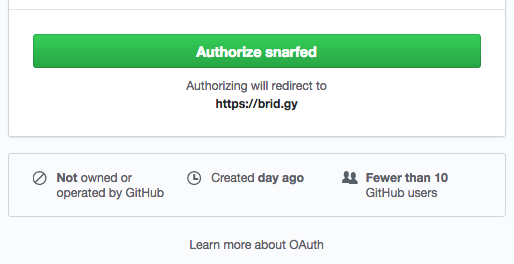
E.g. Bridgy's GitHub permission initially had a "Authorize snarfed" green button (fixed shortly thereafter, says "Authorize bridgy" since 2018-02-20)
(Old example from 2018-02-09.)
The solution is to deploy the application from a GitHub organization account for your application, either with the same name as your application, or whatever organization your application is a part of, that you're asking your users to "trust".
Bridgy for GitHub now does this ("Authorize bridgy" green button), using the https://github.org/bridgy organization. Example prompt below with updated green button. The real prompt has the real logo and omits "local" / "localhost:8080":
Feature Details
Account Recovery
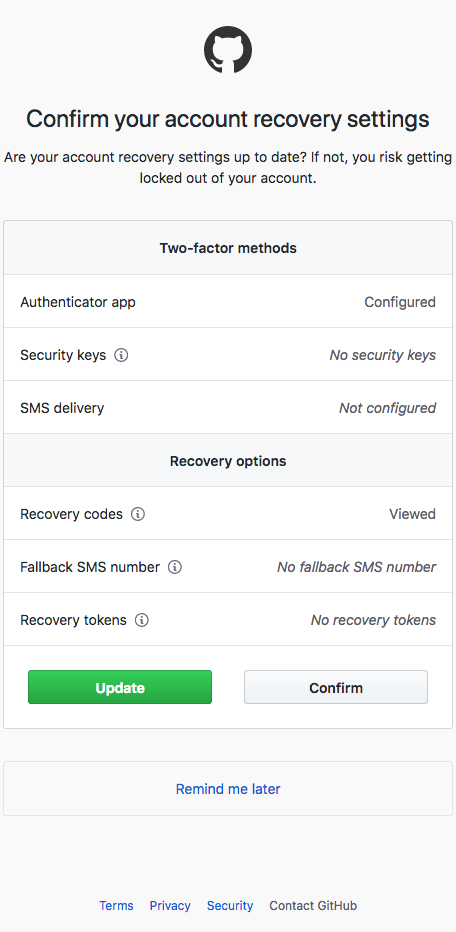
As part of GitHub's Account Recovery feature, starting ~ 2018-07-18, GitHub started putting in a forced interstitial to confirm you account recovery settings, e.g. a page with something like this as its entire content:
Any attempt to load a GitHub URL (assuming you were previously logged in) would result in a temporary redirect to that interstitial. You could still view public GitHub URLs in a browser's "Private Mode" without seeing the interstitial (because you were not logged in).
Note: DO NOT only use "Fallback SMS number" as an account recovery mechanism, for all the reasons documented on the SMS page (tl;dr, SMS is horribly insecure, and fairly trivial for a professional to attack - has already happened to numerous people.)
Self-hosted alternatives
There are some self-hosted alternatives to GitHub. Gitlab and Gogs support issue tracking and project management as well.
- GitLab: full-featured GitHub replacement
- Gogs: full-featured GitHub replacement
- Gitolite: web interface for managing repositories, with fine-grained access controls
- Gitweb: simple web interface for browsing git repositories
- Formerly Gitorious (acquired by GitLab in March 2015)
- Formerly Gitosis (deprecated long ago in favor of gitolite)
- Gitea: Golang, lightweight alternative with many common features
- Forgejo: A fork of Gitea that, among others, powers Codeberg
Brainstorming
Brainstorming about further ways to use GitHub from your IndieWeb site.
POSSE note to GitHub
Plain text notes can be POSSEd to GitHub as a gist.
No known examples of anyone doing this yet.
Be the first and add your permalinks here!
Notable Changes
2019 unlimited free private repos
- 2019-01-07 GitHub blog: New year, new GitHub: Announcing unlimited free private repos and unified Enterprise offering
GitHub Free now includes unlimited private repositories … with up to three collaborators per repository …. Many developers want to use private repos to apply for a job, work on a side project, or try something out in private before releasing it p
Issues
Account reuse is potential security issue
2018-02-07 GitHub allows account deletion, recreation by another party, with library dependency:
- https://twitter.com/weekstweets/status/961304627596623874
- https://donatstudios.com/GithubsTotalSecurityFacepalm
- https://blog.sonatype.com/hijacking-of-a-known-github-id-go-bindata
- Thread: https://twitter.com/francesc/status/961249107020001280
- More discussion: https://www.reddit.com/r/golang/comments/7vv9zz/popular_lib_gobindata_removed_from_github_or_why/
Criticism
DMCA harassment
You can lose your data due to unjustified DMCA takedowns:
- Takedown and Apology
- Github has since improved this process by defining how they are handled better, specifically allowing for the owner to make needed corrections or to move hosts. https://github.com/blog/1908-a-better-dmca-process
DDoS collateral damage
Github is sometimes the target of DDoS attacks, apparently targeted at specific projects. While GitHub seems to be handling the attacks in such a way as to keep access working, this is a vulnerability of any centralized service, that it attracts attacks unrelated to your use of it, that jeopardize your use of it (collateral damage). Most recent first
- 2016-10-21 DDos attack on DYN affects Twitter, Spotify, Reddit, GitHub, effectively taking them all offline.
- 2015-03-26 DDoS attack [1] via unsuspecting browsers executing scripts from (MitM) faked Baidu requests[2].
March 2017 Terms of Service Update
In March 2017, GitHub updated their terms of service. Several people are upset about the change, which may affect GPL and similarly licensed software.
- http://joeyh.name/blog/entry/removing_everything_from_github/
- https://www.mirbsd.org/permalinks/wlog-10_e20170301-tg.htm#e20170301-tg_wlog-10
- Discussion thread: https://news.ycombinator.com/item?id=13766933
Contract with US Immigration and Customs Enforcement (ICE)
Renewed a $200,000 USD contract with ICE in 2019
2019-11-13 : As GitHub’s Conference Begins, Five Employees Resign Over ICE Contract (archived)
- The CEO defended the decision, despite the amount not being “financially material for the company.”
“While ICE does manage immigration law enforcement, including the policies that both GitHub and Microsoft are on record strongly opposing, they are also on the front lines of fighting human trafficking, child exploitation, terrorism and transnational crime,” he wrote, adding that the company would donate $500,000 to non-profits working to combat the effects of Trump’s immigration policies. As of now, the money has not yet been donated.
Friedman’s response has outraged many employees. Nearly 25 percent of the company has signed onto an open letter demanding Friedman cancel the contract, including half of the engineering department.
2019-11-13 : GitHub faces more resignations in light of ICE contract (archived)
“We are not satisfied with GitHub’s now-public stance on this issue,” GitHub employees wrote in an open letter. “GitHub has held a ‘seat at the table’ for over 2 years, as these illegal and dehumanizing policies have escalated, with little to show for it. Continuing to hold this contract does not improve our bargaining power with ICE. All it does is make us complicit in their widespread human rights abuses.”
Downtime
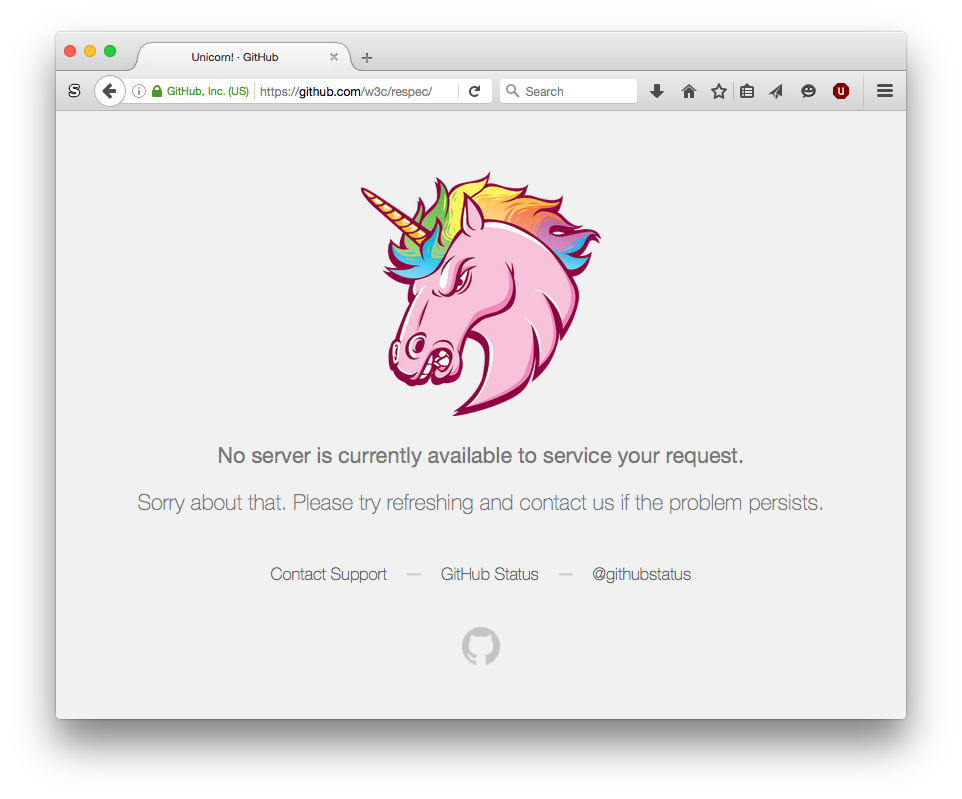
Occassionally GitHub fails to handle requests:
No server is currently available to service your request.
Sorry about that. Please try refreshing and contact us if the problem persists.
2018-10-21 Degraded Service
2018-10-21 GitHub experienced over 24 hours of what they called "Degraded Service".
- Details: 2018-10-30: GitHub Blog October 21 post-incident analysis
During that time GitHub was effectively "down" for many users and use-cases.
- Pages (issues/pull requests) not loading
- Pages (issues/pull requests) out of date
- Editing issues not working
2022-02 degraded performance
- Downtime: https://twitter.com/githubstatus/status/1488953629520367617
- "We are investigating reports of degraded performance for GitHub Actions, Issues, and Pull Requests. https://www.githubstatus.com/incidents/fz1bdbw24y81?utm_ts=1643829183" @githubstatus February 2, 2022
2022-03 service disruptions
GitHub had various outages during the month of March, 2022.
- 2022-03-16…23 various outages
- 2022-03-22 GitHub blog: https://github.blog/2022-03-23-an-update-on-recent-service-disruptions/
- 2022-03-24 GitHub incident: 2022/03/24 Hacker News threads
See Also
- github-pages
- code
- issue tracker
- issue
- commons
- Getting Started
- silo
- GitHub Actions
- Introducing GitHub Actions
- Feature: profile rel-me support to 4 links: https://hachyderm.io/@derekprior/109790473003989772
- "You can now add up to four social account links to your GitHub profile which render with a sprinkling of formatting support for our most popular platforms. Yes, the resulting links links will satisfy Mastodon verification requirements when rendered.To get started, visit your profile and click the "Edit profile" button in the sidebar." @derekprior February 1, 2023
- Criticism: unnecessary amounts of ceremony for common prose editing use-cases: https://chat.indieweb.org/meta/2024-06-26#t1719442233333000 (and following)
- "it's quite satisfying to find a very fixable "hole" like that in Wikipedia and be able to immediately edit save to fix it. No Git(hub) "create a fork" BS, no "Create a patch / pull request" ceremony, no prompted TWO text fields to provide BOTH a summary and a description of the edit, no stupid buttons that say "Merge" or "Squash & Merge" (why?!? so much plumbing BS that the authoring use-case doesn't care about), no "Delete fork" ceremonial" @[tantek] June 26, 2024